Looking for something? Refine your search
- Categories
- Backup
- Cloud
- Computer Forensics
- Computing and CPU Power
- Cryptocurrency
- Damage
- Data Loss Prevention
- Data Recovery Knowledge
- Data Recovery News
- Data Recovery Service
- Data Types
- Database
- Digitization
- Encryption
- Flash Drive
- Hard Disk
- Investing and the Stock Market
- Mac/Apple
- Media
- Mobile Device
- NAS
- Network Security
- Office Documents
- Outreach
- Photos & Images
- RAID
- Ransomware Recovery
- Removable Media
- SAN
- Secure Deletion
- Server
- Services
- SSD
- Storage Industry
- Tape
- Uncategorized
- Video
- Tags
- actuator
- Apple
- backup
- bitcoin
- breach
- clean room
- clone
- computer forensics
- cryptocurrency
- cybercrime
- data recovery software
- data recovery tips
- decision tree
- EEPROM
- encryption
- ethereum
- exploit
- financial records
- fire damage
- flood
- guide
- hard drive data recovery
- hard drive failure
- hard drive manufacturers
- head ramps
- helium
- how to
- hurricane
- iOS
- landing zone
- leak
- Mac
- Mac OS
- machine learning
- macos
- Midwest
- migration
- music data recovery
- NAND
- NFT
- NVRAM
- operating system
- OS X
- parts
- password
- PCB
- Phoenix
- power surge
- RAID
- ransomware
- rebuilt
- SATA
- SaveMyFiles
- SSD
- statistics
- storms
- tornadoes
- TRIM
- video conversion
- virus
- water damage
- wildfires
- windows 10
- windows 10 guide
SamSam Ransomware Infection And Decryption Services
SamSam ransomware (also known as Samas, SamSamCrypt, and MSIL) is a quickly evolving type of malware that targets hospitals, municipalities, and other large organizations. After installing malicious software through compromised servers, the hackers encrypt network files, making them unusable, and...
April 11, 2018
City of Atlanta Hit by SamSam Ransomware
A ransomware attack on the city of Atlanta on Mar. 22 has left officials scrambling to provide services to residents. Many critical services, like public-safety and wastewater treatment, have been unaffected. Meanwhile, other systems have ground to a halt or...
April 1, 2018
Only Half of Ransomware Payments Resulted in Decrypted Files
A report from a leading research firm found a startling statistic for 2017: only half of ransomware victims who paid a ransom were able to successfully decrypt their files. These findings and others in the report offer even more incentive...
March 21, 2018
SamSam Ransomware Infects CDOT
SamSam ransomware has infected thousands of computers at the Colorado Department of Transportation. Over 2,000 employee computers were shut down to stop the spread of the malware after it was discovered on Feb. 21, and systems are still not back...
March 19, 2018
2017 Ransomware Recap
Ransomware became a household name in 2016. As hackers extorted ransoms from hospitals, universities, and other groups in return for files, the public became aware of how vulnerable devices are in this connected age. Even with the awareness of this...
January 4, 2018
Ransomware Market Expands as Healthcare Industry Continues Feeling the Effects
A computer security company determined that the dark-web ransomware market has grown by 2,500 percent from 2016 to 2017. The company, Carbon Black, credits that expansion to the relative anonymity of Bitcoin and Tor as well as the lucrative return-on-investment...
October 25, 2017
The 4 Most Game-Changing Ransomware Attacks
Every week, new strains of ransomware infect computers or are spotted by security researchers while still in development. Most of them are small-scale operations that attract little attention. Every once in a while, a new malware will make headlines based...
October 9, 2017
Locky Creators Tweak Variants To Evade Detection
Locky ransomware first appeared in February 2016 using a simple but ingenious social engineering method. The distributors sent thousands of emails around the world with an infected Microsoft Word document that appeared as gibberish when opened. The message, “Enable macro...
October 4, 2017
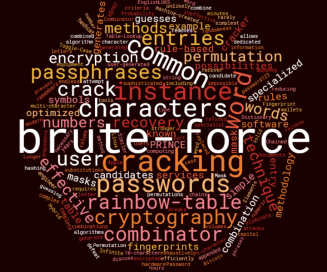
Cracking Passwords: 11 Password Attack Methods (And How They Work)
At Datarecovery.com, we frequently recover lost passwords for everything from Word documents and RAR files to encrypted Linux volumes (LUKS encryption) and Bitcoin wallets. Our customers often ask about our methods; do we simply try every possible password, or is...
September 18, 2017
EV Ransomware Targets WordPress Sites
A new strain of ransomware targets websites created through WordPress. The malware encrypts a web server’s files making them inaccessible. Experts have named the malicious software “EV” because it appends files with “.ev” after encrypting them. The ransomware is...
September 12, 2017