“Phishing” is a common term used for a specific type of malicious attack, but it’s often misused in  popular press. The term seems somewhat self explanatory — “phishing” sounds like “fishing,” so people assume that involves setting out bait and waiting for a computer user to make a mistake.
popular press. The term seems somewhat self explanatory — “phishing” sounds like “fishing,” so people assume that involves setting out bait and waiting for a computer user to make a mistake.
That description is fairly accurate, but phishers typically use specific tools to accomplish their goals. In a typical scenario, a phishing email will claim to be from a reliable source — for instance, a credit card company — and attempt to gain the target’s trust by linking to an apparently legitimate website.
Click on the link in a phishing email, and you might see a website that’s totally indistinguishable from a legitimate website. This isn’t difficult to accomplish; a phisher can simply download all of the web pages from the real site, then replace or remove any links that don’t serve their purposes. Targets are prompted to enter personally identifiable information such as their credit card numbers, social security numbers, or login credentials.
In some cases, phishing attacks won’t link to a website. Instead, they’ll prompt the user to download an attachment. Once again, the attachment seems totally legitimate; it might appear to be a Word document or PDF, but once deployed, it can disable files on the target’s computer (read our articles on ransomware attacks for more information on this method of attack).
Some important considerations to keep in mind when reading about phishing attacks:
Phishing is Often Sophisticated – When most people hear about phishing attacks, they assume a low level of sophistication. Most people have received an email that looks something like this:
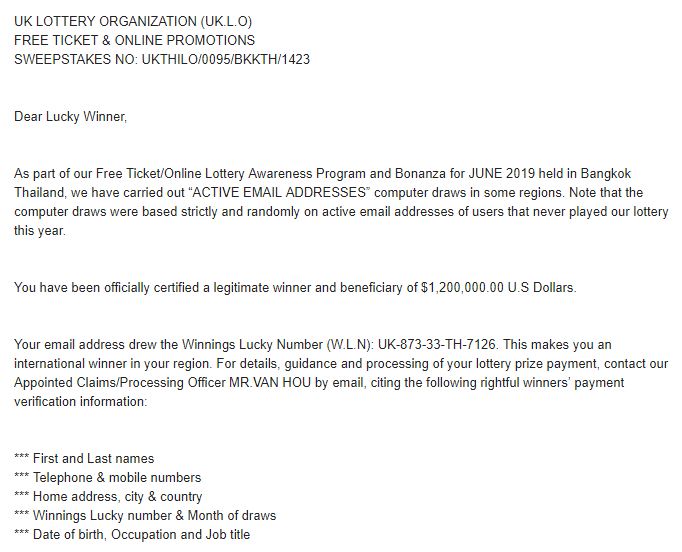
An example of a spam email used to gather personal information.
In these cases, the scam is obvious — and made more obvious by numerous misspellings and grammar mistakes. This is the simplest form of phishing, and it’s easy to avoid.
In some cases, however, scammers perform detailed reconnaissance on their targets before attempting a phishing attack. This is especially common when the target isn’t a single computer user, but rather a network. In many cases, a phishing attack can easily take down an entire series of networked computers if it can gain access to a single machine, so the attackers will gather information about their targets before attempting infiltration.
You might receive a phishing email, text, or social media message that contains detailed information that hackers shouldn’t be able to find easily — your name, family members’ names, addresses, business contacts, and other personal information. This is called a spear phishing attack due to its high level of focus.
In other cases, phishers compromise a legitimate website, using DNS cache poisoning to send visitors to a fraudulent site. This is called pharming, and it can be extraordinarily effective. Pharming a major site for a few minutes can give attackers thousands of names, addresses, and login credentials.
Methods of Engagement Vary – While most phishing attacks use email, some use text messages and social media. These links are no safer than the links you’d see in an email — and, in fact, many mobile devices have poorer defenses against attackers.
In recent years, we’ve heard from customers who typed in a link manually after receiving a phone call from an apparently trustworthy source. In these attacks, they might get a call from the “fraud prevention department” of their credit card company. The scammer warns them not to give any information over the phone, as it isn’t safe.
Instead, victims are urged to go to a secure website to enter their information and verify their purchases. The sites, of course, are fake, but they allow attackers to harvest crucial information.
Consider Every Link a Threat – To stay safe, computer users need to stay skeptical. Even if an email apparently comes from a reliable source, it’s important not to open links unless you can directly communicate with the sender and verify that the links are legitimate.
Watch out for some of the telltale signs of a phishing email:
- Unusual subdomains not associated with major websites.
- Bad grammar and misspellings.
- Links on the site that seem to point nowhere.
- Unexpected attachments, regardless of their source.
- Requests to relay personal information through email.
Every business should train employees to recognize phishing attacks and set strict rules for opening links and attachments. Even with appropriate training, however, some attacks will be successful — that’s why it’s important to back up every system and develop an effective disaster recovery plan.
If you’re the victim of a phishing attack, or if you’d like more information to create a disaster recovery plan for your business, contact our phishing experts at 1-800-237-4200.

