Looking for something? Refine your search
- Categories
- Backup
- Cloud
- Computer Forensics
- Computing and CPU Power
- Cryptocurrency
- Damage
- Data Loss Prevention
- Data Recovery Knowledge
- Data Recovery News
- Data Recovery Service
- Data Types
- Database
- Digitization
- Encryption
- Flash Drive
- Hard Disk
- Investing and the Stock Market
- Mac/Apple
- Media
- Mobile Device
- NAS
- Network Security
- Office Documents
- Outreach
- Photos & Images
- RAID
- Ransomware Recovery
- Removable Media
- SAN
- Secure Deletion
- Server
- Services
- SSD
- Storage Industry
- Tape
- Uncategorized
- Video
- Tags
- actuator
- Apple
- backup
- bitcoin
- breach
- clean room
- clone
- computer forensics
- cryptocurrency
- cybercrime
- data recovery software
- data recovery tips
- decision tree
- EEPROM
- encryption
- ethereum
- exploit
- financial records
- fire damage
- flood
- guide
- hard drive data recovery
- hard drive failure
- hard drive manufacturers
- head ramps
- helium
- how to
- hurricane
- iOS
- landing zone
- leak
- Mac
- Mac OS
- machine learning
- macos
- Midwest
- migration
- music data recovery
- NAND
- NFT
- NVRAM
- operating system
- OS X
- parts
- password
- PCB
- Phoenix
- power surge
- RAID
- ransomware
- rebuilt
- SATA
- SaveMyFiles
- SSD
- statistics
- storms
- tornadoes
- TRIM
- video conversion
- virus
- water damage
- wildfires
- windows 10
- windows 10 guide
Qilin Ransomware Threat Analysis: Rust-based Attacks on Healthcare
The average cost of a healthcare data breach reached $10.1 million in 2024, the highest of any industry for the 14th consecutive year, according to the IBM Cost of a Data Breach Report. It’s likely that that number climbed...
March 6, 2026
5 Common Ransomware Attack Vectors
Ransomware enters a network through specific entry points known as attack vectors. Phishing, Remote Desktop Protocol (RDP) exploits, and software vulnerabilities are the most frequent culprits. In this guide, we’ll explore five attack vectors, along with defense tactics to limit...
January 12, 2026
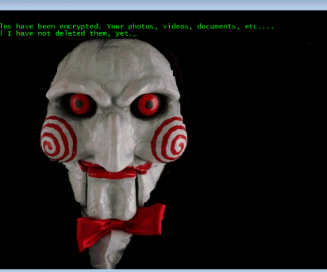
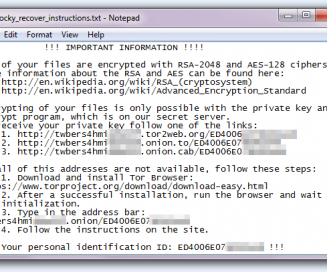
Ransomware Identification: How to Determine Which Variant Has Hit Your Network
According to the 2025 Data Breach Investigations Report from Verizon, ransomware was present in 44% of all analyzed breaches over the past year — a sharp increase from 32% in 2024. When an infection occurs, the first step is to...
January 1, 2026
Akira Ransomware: Ransomware Threat Assessment
Akira is a sophisticated, human-operated Ransomware-as-a-Service (RaaS) operation that targets both Windows and Linux systems. It frequently exploits vulnerabilities in Virtual Private Networks (VPNs) to encrypt critical data and exfiltrate sensitive files for double extortion. If you have discovered files...
November 26, 2025
U.S. Treasury Sanctions Russian Ransomware Money Laundering Network
The U.S. Department of the Treasury has taken decisive action against the financial infrastructure fueling the global ransomware epidemic. Per AP News, the Office of Foreign Assets Control (OFAC) has sanctioned Russian national Sergey Ivanov and the payment processor...
November 20, 2025
Washington Post Data Breach: Clop Ransomware Gang Remains Active
The Washington Post has confirmed it was the victim of a significant data breach, exposing the highly sensitive personal and financial information of nearly 10,000 current and former employees and contractors. The attack has been linked to the Clop ransomware...
November 14, 2025
What Are Double-Extortion and Triple-Extortion Ransomware Attacks?
Double-extortion ransomware is an attack where criminals both encrypt your files and steal (exfiltrate) your data. Triple-extortion simply adds a third layer of pressure such as a Distributed Denial-of-Service (DDoS) attack or harassment to your clients or staff. It’s simply...
November 1, 2025
What Is the CVE-2024-1086 Linux Flaw (And Why Is It Used in Ransomware?)
A decade-old bug in the Linux kernel is now being actively used by ransomware groups to gain full root control of a server, according to a new warning from CISA. This vulnerability, tracked as CVE-2024-1086, is exceptionally dangerous because it...
October 31, 2025
When Is Ransomware Recovery Possible?
In 2024, about 59% of organizations were hit by ransomware, per a report from Sophos — and while that number is shocking, it’s actually slightly lower than the numbers for 2023. For bad actors, ransomware is a lucrative business, and...
October 24, 2025
How to Recover a Lost Cryptocurrency Wallet
Recovering a lost cryptocurrency wallet depends entirely on whether you have your seed phrase. This 12 to 24-word phrase is the master key to your assets, and if you have it, the recovery process is generally straightforward. If you have...
August 20, 2025