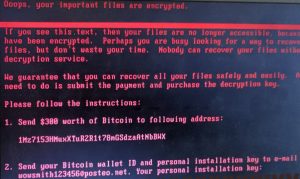
A screenshot of the Petya variant’s ransomware message.
An immediate response to a ransomware attack requires isolating infected systems from your network to prevent the encryption from spreading to backups and cloud storage. Effective recovery depends on preserving system logs and avoiding the temptation to run unverified decryption tools, which can cause permanent data corruption.
Below, we’ll outline a strategic plan for containment, variant identification, and professional data restoration tailored for organizations in the St. Louis metropolitan area. If your organization is experiencing a ransomware incident, we’re here to help. With local offices in Edwardsville, Illinois — 25 minutes from downtown St. Louis — Datarecovery.com is uniquely qualified to provide threat assessment, mitigation, and data recovery services.
Call 1-800-237-4200 to speak with an expert or submit a case online.
Immediate Ransomware Containment Strategies
When ransomware impacts key systems, it’s important to isolate the infected segment of your network as quickly as possible.
- Disconnecting affected servers and workstations from the local area network (LAN) and the internet prevents the ransomware from communicating with the attacker’s command-and-control (C2) servers.
- We suggest physically unplugging Ethernet cables rather than relying on software-based shutdowns: some malware can intercept shutdown commands.
- Preserving the current state of infected machines is equally important for later forensic analysis. Avoid rebooting or wiping machines immediately, as volatile memory (RAM) may contain decryption keys or fragments of the ransomware’s execution path.
Contrary to popular belief, successful ransomware data recovery is possible in many circumstances. However, some variants use sophisticated encryption, which can limit results; isolating the affected system is absolutely critical.
Identifying the Ransomware Variant
Ransomware strains (or variants) operate differently. Some only encrypt the first section of targeted files, which can make data recovery fairly straightforward — others use extremely sophisticated methods that render data permanently unrecoverable.
Recent incidents in the St. Louis area such as the 2024 cyberattack on Francis Howell School District, show how quickly disruptions can force entire systems offline. By identifying whether you are dealing with a common strain like Akira or Qilin, we can assess the viability of decryption without engaging with the attackers.
In our laboratories, we analyze the file headers and ransom notes to pinpoint the encryption method used. Keep track of the following:
- The types/formats of files targeted;
- The location of those files;
- The text and design of any ransom notes (screenshots are helpful); and
- The approximate size of the impacted files.
Knowing the variant is essential because different groups use different attack vectors. Some older or poorly implemented strains have known vulnerabilities.
How Ransomware Data Recovery Works
 To restore operations for schools and non-profits, we set two goals: Restore the affected systems and ensure that the infection has been completely isolated and eliminated. Following a strategic recovery plan helps avoid a secondary infection, which occurs when backdoors are left behind by the initial attackers.
To restore operations for schools and non-profits, we set two goals: Restore the affected systems and ensure that the infection has been completely isolated and eliminated. Following a strategic recovery plan helps avoid a secondary infection, which occurs when backdoors are left behind by the initial attackers.
At Datarecovery.com, we provide St. Louis-area institutions with a local advantage through our full-service laboratory in Edwardsville, Illinois. Our team utilizes purpose-built systems to bypass complex encryption and repair damaged databases that standard IT departments are not equipped to handle.
Every case begins with a risk-free evaluation. If your St. Louis school or non-profit is currently facing a data crisis, we are ready to assist. Contact our specialists at 1-800-237-4200 or submit a case online for immediate support.





