Most ransomware attacks target desktop computers, servers, and high-value storage networks — but in recent years, a growing number of attacks have targeted smartphones and other mobile devices.
Below, we’ll look at a few examples of how mobile ransomware works. We’ll also provide tips for preventing malware from endangering your data.
Can ransomware infect an iPhone or Android phone?
To date, all mobile ransomware has targeted Android devices. iOS devices like iPhones are highly resistant to malware, but malicious users have exploited vulnerabilities to trick users into believing that their devices were infected with ransomware.
While Android mobile operating systems include safeguards to protect against malicious software, those protections have limits, particularly when attackers use social engineering to trick users into downloading files.
Notable recent incidents:
- In 2014, the Koler “police” ransomware began to spread using pornographic networks. Android users are tricked into downloading a fake .apk file, which encrypts files and demands a ransom of $100-$300. By some estimates, Koler has infected more than 200,000 Android devices.
- Doublelocker is a Trojan that infects Android devices, changing their PINs and encrypting data to prevent access. It is typically distributed as a fake Adobe Flash Player. Victims are tricked into providing the malware with administrator rights and permissions.
- AndroidOS/MalLocker.B uses social engineering to lure victims into installing fake versions of games or popular apps. Instead of encrypting files, this ransomware family prevents the user from accessing their device by forcing a ransom note onto every screen.
To protect your phone from ransomware, follow these steps.
Cybercriminals use sophisticated methods to install malware and extort users. If you store important data on your phone (and realistically, that’s true for nearly every smartphone user), you’ll need to protect yourself. Some quick steps to keep your device secure:
1. Back up your data.
The best practice is to maintain at least three copies of every important file. However, even a single backup will provide enormous protection — provided that your backup isn’t prone to infection.
Here’s a guide from Google for backing up data manually on an Android device. For Apple iPhones and iPads, this guide explains the process for using iCloud. In addition to cloud backups, consider copying important data (such as pictures, videos, and contacts) to your PC or Mac on a regular basis.
2. Don’t install apps unless you can verify the source.
Most Android ransomware variants infect devices by posing as free games, utilities, or video players. By default, the Android operating system blocks users from installing .apk files from unknown sources, but users can disable this protection.
The safest course of action: Never download an .apk file through your phone’s web browser, and never open email attachments if you’re not completely confident in the contents. Only install apps using the Google Play store or another trusted app store.
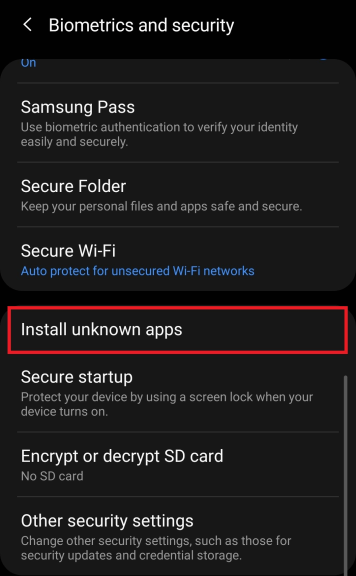
If you do need to install an .apk manually, make sure you trust the source. Check that the website has valid security certificates. After installing the app, head to Android Settings -> Biometrics and Security and change the “Install unknown apps” settings back to the default.
3. Keep your device updated.
Malware often spreads by taking advantage of security vulnerabilities within apps or the mobile operating system.
Make sure your phone updates its operating system automatically. Here’s a guide to enabling auto-updates on Android, and here’s a guide for enabling automatic updates on iOS devices.
Android users should also enable automatic updates on apps downloaded from the Google Play store.
4. If your smartphone is infected with ransomware, have a game plan.
If you believe your phone is infected with malware, take notes about any symptoms, including actions that may have led to infection (such as downloading an APK file or downloading email attachments). If your phone displays a ransom note, take a picture with another device or write down the note in its entirety.
Decryption tools exist for many common Android ransomware variants. If you have a strong working knowledge of the Android operating system, NoMoreRansom.org is a trustworthy resource for finding free decryption tools.
However, we recommend working with an experienced ransomware recovery firm to maximize your chances of a successful result. To learn more, contact our team at 1-800-237-4200 or click here to set up a case online.
