
Ransomware attacks continue to threaten businesses, local governments, and nonprofit organizations — and the trend is unlikely to change anytime soon.
According to public records, more than 400 city and county governments have sustained ransomware attacks since 2014. Private entities don’t always report attacks, but the European Union Agency for Cybersecurity (ENISA) reported a 150% rise in ransomware infections between April 2020 and July 2021.
When bad actors successfully deploy ransomware, your options are limited: Restore the data from a backup, pay the ransom, or look for professional ransomware data recovery options.
As a leading provider of ransomware recovery services, Datarecovery.com can provide the guidance your organization needs to take appropriate action. Before attempting ransomware recovery, keep these tips in mind.
1. Understand the extent of the ransomware infection.
In a disaster, many enterprises take immediate action to restore mission-critical systems — but quickly restoring from a backup system can have unintended consequences.
Many ransomware variants target backup devices. Attackers understand that the best defense against ransomware infection is a strong disaster recovery plan, and modern variants often have a “dormant stage.” If the ransomware spreads through backups (and occasionally, archival systems), attempting restoration could prevent a quick resolution.
The best practice is to evaluate all data storage systems immediately. Document your assessment and attempt to identify the date and source of the infection. Isolate networks and data management devices, and never attempt to restore data (even when backups are stored on air-gapped media) until the assessment is complete.
2. Remember, some ransomware infections can be easily resolved.
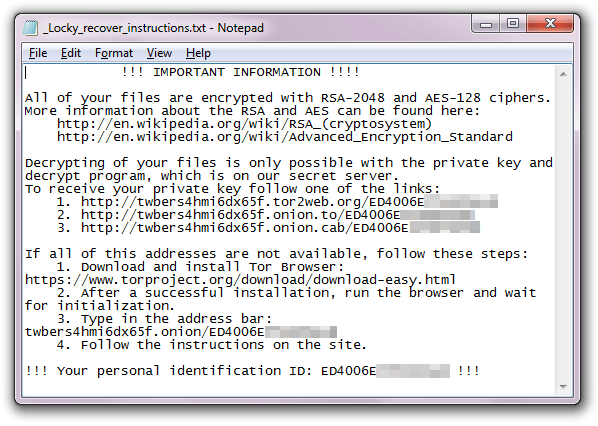
Ransomware works by encrypting data, and some variants use encryption methods that can be easily bypassed. White-hat hackers have created numerous tools for addressing common infections, and with help from a professional data recovery company, you may be able to restore encrypted data without losing much uptime.
 Common ransomware variants with publicly available decryptors include:
Common ransomware variants with publicly available decryptors include:
- Prometheus
- LockFile
- Ziggy
- Synack
- Avaddon
- Judge
- AtomSilo
This is not a comprehensive list. Free decryption tools are available at the No More Ransom Project.
However, we recommend caution when using free decryption tools: For enterprise-level systems, some tools may require advanced restoration techniques — and on complex systems, you may not get a second chance for a loss-free recovery. Work with an experienced ransomware partner to ensure the best possible recovery.
3. Targeted ransomware attacks require specialized resources.
Some ransomware variants are designed to target specific architectures. Typically, data recovery is not possible using publicly available decryption tools.
The BlackMatter ransomware group, which claims to be the successor to the infamous Darkside and REvil groups, targets corporate networks with revenue of $100 million or more. “Ransomware-as-a-Service” (RaaS) groups offer compensation to individuals within large organizations, creating backdoors that increase their chances of successful infiltration.
Common targets for ransomware groups include:
- Retail and e-commerce companies
- Universities and other educational institutions
- Professional and legal service providers
- Central, state, and local government offices
- Software as a Service (SaaS) providers
Targeted attacks often carry ransoms of $100,000 or more. Data recovery solutions vary depending on the extent of the attack, the organization’s IT architecture, and the sophistication of the ransomware encryption.
4. Paying the ransom doesn’t always prevent data loss.
When ransomware targets mission-critical systems, the obvious solution is to pay the ransom. Unfortunately, this isn’t a fool-proof strategy.
According to one 2021 report, only 9% of people who pay ransomware attackers get all of their data back. Ransomware isn’t designed for restoration, and the encryption process may render important files (such as databases) unusable.
Paying ransoms also provides bad actors with powerful incentives to pursue additional attacks. In numerous cases, companies have sustained multiple ransomware infections within short periods of time — often from the same group of attackers.
The best defense against ransomware is a strong disaster recovery strategy.
With air-gapped backups, most organizations can avoid significant data loss due to ransomware infection. By continually monitoring for signs of infection, you can execute your disaster recovery strategy swiftly — but even with a robust defense, attacks can compromise key systems.
The second-best defense is an experienced data recovery partner. Datarecovery.com operates full-service laboratories with proprietary decryption tools, and our engineers have decades of combined experience with enterprise systems. As the industry’s leading ransomware recovery provider, we have the technical resources and expertise to get your data back quickly — limiting downtime in a disaster.
When malicious attacks affect your business, our team can help. Call 1-800-237-4200 to discuss ransomware recovery options.





